Managed Security Services
Powered by ZERO TRUST
Protect your organization with the strength of Zero Trust, delivered as a fully managed service. With ON2IT’s Managed Security Services, you gain 24/7 protection, expert response capabilities, and complete visibility—without the need to build your own Security Operations Center.

Effortless Security Operations
Managed Security
Built on Zero Trust
ON2IT delivers the industry’s most complete stack of technology, processes, and cybersecurity experts – all offered through a single managed cloud service. We handle your security operations, so you can stay focused on what truly matters: running and growing your business.
Why Managed Security?
Stay Focused on Your
Core Business
Running a fully effective cybersecurity operation requires substantial time, budget, and specialized talent. Do you have the resources for a 24/7 Security Operations Center?
Many organizations attempt to manage IT security in-house, but struggle with hiring, retaining talent, and staying ahead of evolving threats. The cybersecurity skills gap remains a challenge, and budgets are often stretched thin. ON2IT’s Zero Trust as a Service guarantees reliable security outcomes at a predictable cost—so you can focus on growth with confidence.
Fully Managed SOC Services
mSOC™: 24/7 Detection, Response & Prevention
Our mSOC™ delivers round-the-clock Managed Detection & Response, combined with robust prevention and compliance services—all integrated into our unique Zero Trust as a Service platform.
SOAR
ON2IT’s in-house built orchestration and automation platform
24/7 SOC
Your continuously operating security conscience
CIRT
A ready-to-deploy team of incident response experts
XDR
Advanced detection and extended visibility across systems
SIEM
Real-time monitoring, log analysis, and audit compliance
Unified Zero Trust Security Architecture
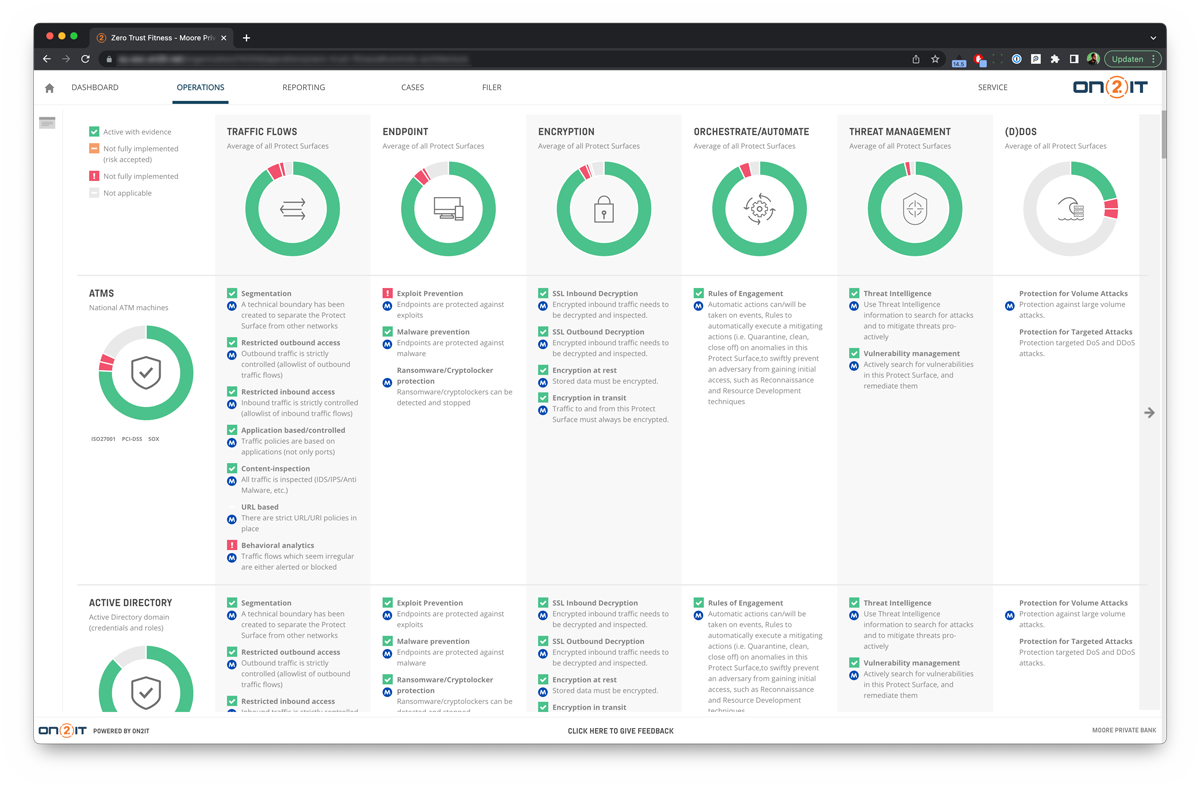
AUXO™: The Core of ON2IT’s Managed SOC
The ON2IT mSOC™ is powered by AUXO™, our proprietary extension of SOAR that blends the best of SIEM, SOAR, and MDR. It provides all the essential Zero Trust building blocks—delivered as a fully managed, scalable service.
With AUXO™, you can:
Monitor the real-time health of your IT security
Detect and investigate threats proactively
Adjust policies and optimize your defense posture
Receive actionable recommendations for remediation and resilience
AUXO™ makes true Zero Trust implementation practical and affordable.
Enhance and Simplify Security Operations
AUXO™ Zero Trust Platform: Key Features
Take full control of your cybersecurity program with AUXO™’s modular components—built for visibility, action, and compliance:
Controls Management
24/7 insight into control health and effectiveness
Protect Surface Management
Identify and protect critical data assets
Event Management
Significantly reduce false positives through smart filtering
Incident Management
Rapid response with expert-led investigations
Improvement Management
Learn from incidents and optimize configurations
Compliance Management
Real-time dashboards for compliance and auditing
Purpose-Built Managed Solutions
Tailored Security Services for Every Layer of IT
Explore our specialized managed security offerings designed for modern enterprise environments:
Find out how ON2IT can secure your complete digital ecosystem.


